
The Yacht, the Princess, and the Ghost in the Network
It was March 4th, 2018. Somewhere in the Arabian Sea, a yacht cut quietly through dark waters. On board was Latifa Al Maktoum — daughter of Sheikh Mohammed, the ruling emir of Dubai — fleeing what she described as years of imprisonment, beatings, and solitary confinement. With her were a Finnish martial arts instructor and a former French intelligence officer, Hervé Jaubert, serving as captain. For eight days they’d sailed undetected toward India. Freedom felt close.Then, without warning, a dark vessel emerged from the night. Laser sights swept across the deck. Armed agents boarded the yacht and seized Latifa, returning her to Dubai.She had never posted her location. She had never called home. She had done everything right.
But her captain’s phone had been compromised — not through malware, not through a spy in their midst — but through an invisible, decades-old backdoor baked into the very infrastructure of the global phone network. His location had been pinpointed to within meters. The attackers never touched his device.The exploit was SS7.
Table of Contents
What Is SS7?
Signaling System No. 7 (SS7) is a set of telephony protocols developed in 1975 and widely deployed from 1980 onward. It is the backbone of global telecom — the protocol stack that handles everything behind the scenes when you make a call, send an SMS, or roam abroad.
When you land in a foreign country and your phone seamlessly connects to a local network, SS7 is what makes that possible. Your home carrier and the foreign carrier exchange authentication and billing data over SS7 to verify your identity and authorize the connection. When someone calls your number, SS7 is what routes that call to whichever cell tower you’re currently connected to, wherever in the world you might be.
At its core, SS7 defines a series of messages — structured commands sent between network nodes — that control call setup, teardown, SMS delivery, location updates, and subscriber authentication. These messages travel not over the voice channel, but over a separate out-of-band signaling network, a private digital backbone connecting telecom operators globally.
Key SS7 message types relevant to attacks include:
- Send Routing Info (SRI) — Queries a subscriber’s home network for their current location and routing data.
- Send Routing Info for SM (SRI-SM) — The SMS variant; used to find where to deliver a text message.
- Provide Subscriber Info (PSI) — Requests the current cell tower (and by extension, location) of a subscriber.
- Insert Subscriber Data (ISD) — Can update routing information stored in the network, redirecting calls or messages.
- Anytime Interrogation (ATI) — Perhaps the most alarming: allows any connected node to query the location and IMSI of a subscriber at any time, with no authentication requirement. The name is apt. It was eventually deprecated, but only after years of abuse.
The Architecture: A Walled Garden With Too Many Gates
When SS7 was designed, the global telecom landscape consisted of a handful of large, state-backed operators with deeply trusted relationships. The security model was essentially: if you’re in the network, you’re trusted. This is sometimes called the walled garden model.
To participate in SS7, an operator is assigned a Global Title (GT) — a unique address used to identify the source of SS7 messages, analogous to an IP address on the internet. Operators typically only accept messages from GTs with which they have established agreements, creating a nominally closed club.
The problem? The garden now has thousands of gates.
Today there are over 1,200 operators and 4,500 networks globally with SS7 access. These range from traditional carriers to virtual network operators, bulk SMS providers, roaming brokers, and aggregators. Many of these entities sell or sublicense their GT access. A trusted GT from a legitimate operator in one country can, thanks to bilateral roaming agreements, be used to send messages that are accepted by networks worldwide.

How SS7 Attacks Work
An SS7 attack usually begins with a phone number. Attackers send signaling requests to the target’s home network to retrieve the IMSI (International Mobile Subscriber Identity) linked to the SIM card. With this identifier, attackers can send additional SS7 messages that allow them to intercept calls, redirect SMS messages, or determine which cell tower the phone is connected to. Since these requests occur inside telecom infrastructure, the victim’s device receives no warning or notification.
Step 1 — Infiltrate: Get Inside the Network
Acquire SS7 access via a legitimate or corrupted operator. This is the prerequisite for everything that follows. As noted above, this is a monetary problem, not a technical one.
Step 2 — Gain Trust: Harvest the IMSI
A phone number alone isn’t enough. What you need is the target’s IMSI (International Mobile Subscriber Identity) — a unique 15-digit identifier tied to their SIM card, not their phone number. The IMSI is the real key to the network.
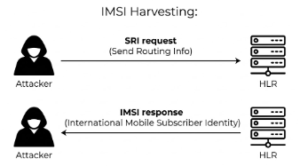
To get it, an attacker sends an SRI or SRI-SM request to the target’s home network. These messages are designed for legitimate routing purposes — but the response includes the IMSI. Many networks will return this data to any trusted GT that asks, no questions asked.
With the IMSI in hand, the attacker can now impersonate the network itself when targeting the subscriber.
Step 3 — Attack: Three Vectors
A) Call Interception
Using the harvested IMSI, an attacker sends an Insert Subscriber Data (ISD) message to the target’s home network, updating the routing instructions to redirect incoming calls to an attacker-controlled node. The network now believes the target is “roaming” and routes all calls accordingly. The target’s phone never rings. The attacker answers, can forward the call to the real recipient to avoid suspicion, and records everything in between. All that’s needed to initiate this: a phone number.
B) SMS Interception / 2FA Theft
The same rerouting technique applies to SMS. By tricking the network into thinking the target is roaming, all inbound SMS — including one-time passwords for two-factor authentication — are delivered to the attacker’s GT instead. The window is brief (it resets when the subscriber’s phone reconnects to a real tower), but a few seconds is enough to receive a 2FA code, log into an account, and change credentials. SMS-based 2FA, which remains the default for most banking and many web services, is entirely defeated by this.
C) Location Tracking
SS7 location tracking doesn’t use GPS. It works by querying the network for which cell tower the target’s IMSI is currently registered to. In dense urban areas with many overlapping towers, this can resolve locations to within 100 meters. A more precise variant — timing advance triangulation — calculates signal travel time from multiple towers to pinpoint a location on a 2D plane.
Crucially, SS7 location requests generate no notification on the target’s device. There is no ping, no battery drain, no indicator of any kind. The request is invisible.
This is precisely how the captain’s yacht was found. In a five-minute window, attackers sent at least seven IMSI-harvesting requests and at least four location tracking requests using multiple GTs leased across different countries — a textbook multi-vector SS7 operation. Most requests were blocked by firewalls, but a sixth GT — likely a domestic US one — sent requests that were never logged, meaning they likely succeeded.
“The phone was never hacked. The device was never touched.The only thing compromised was the network the entire world trusts.”
